As of January 2019 this is no longer necessary as the Intune Company Portal app is now included in the default list of protected apps.
Organizations using Windows Information Protection (WIP) may experience issues accessing the Intune Company Portal app. Fortunately, exempting Intune Company Portal app and any other application from a WIP policy is straight forward.
To learn more about creating Windows Information Protection policies please visit: https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protection/create-wip-policy-using-mam-intune-azure
Let’s get started
By exempting an application the following pertains:
If you’re running into compatibility issues where your app is incompatible with WIP, but still needs to be used with enterprise data, you can exempt the app from the WIP restrictions. This means that your apps won’t include auto-encryption or tagging and won’t honor your network restrictions. It also means that your exempted apps might leak.
Source: https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protection/create-wip-policy-using-mam-intune-azure#add-apps-to-your-allowed-apps-list
Since the Intune Company Portal App doesn’t store any sensitive company data, exempting it shouldn’t be an issue, however always check in with your security team to make sure.
The first step to exempting the Intune Company Portal App for Windows is to locate the app in the store. I’ve done this for you below and even though the app may be accessed from the consumer and business store, all we really care about is the AppID at the end, i.e. “9wzdncrfj3pz”.
As we can see, the AppID is the same regardless of what portal it was accessed from:
Windows Store Intune Company Portal app: https://www.microsoft.com/en-us/store/p/company-portal/9wzdncrfj3pz
Windows Store for Business Intune Company Portal app: https://businessstore.microsoft.com/en-us/store/details/company-portal/9wzdncrfj3pz
Creating the WIP exemption policy
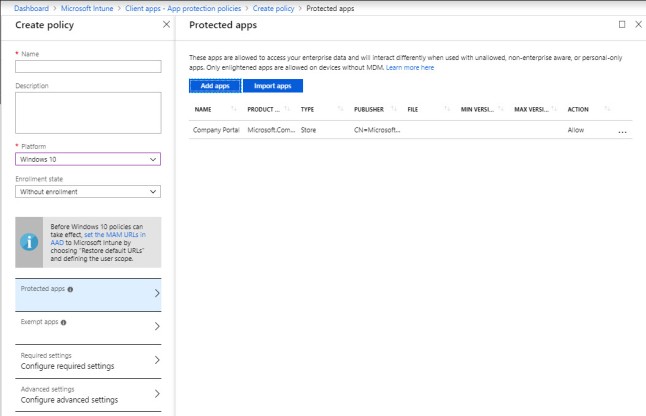
To create an app policy within Intune to exempt the Intune Company Portal app navigate to portal.azure.com à Intune à Mobile Apps à App protection policies à Add a policy
-
Give the policy a name and select Exempt apps
-
Select Add apps
-
From the drop-down menu select Store apps
At this point you’ll need to have some information handy about the app. Fortunately, there is an easy method of extracting this data using the URL below. I’ve already accessed the URL below; however, you can do this for any store app to find the name, publisher info, and product name.
Access following and replace the ID with the ID of the app you’d like to exempt, in this case, the Intune Company Portal app ID: 9wzdncrfj3pz
https://bspmts.mp.microsoft.com/v1/public/catalog/Retail/Products/9wzdncrfj3pz/applockerdata
For more details about accessing app package info please visit: https://docs.microsoft.com/en-us/windows/client-management/mdm/get-product-package
The following is the output you’ll see in the browser in JSON format:
{
“packageFamilyName”: “Microsoft.CompanyPortal_8wekyb3d8bbwe”,
“packageIdentityName”: “Microsoft.CompanyPortal”,
“windowsPhoneLegacyId”: “0b4016fc-d7b2-48a2-97a9-7de3b5ea7424”,
“publisherCertificateName”: “CN=Microsoft Corporation, O=Microsoft Corporation, L=Redmond, S=Washington, C=US”
}
Now that we have the JSON information about the Intune Company Portal store app (using the URL above), we need to add that data to the policy as shown below.
Once finished adding the information, select OK and assign the policy. On the Windows device, either wait for your devices to sync with Intune of force a sync from Settings à Accounts à Access work or school.
Once the policy updates you’ll be able to access the Intune Company Portal app:
If you’re interested, I go into detail about WIP a previous post: https://blogs.technet.microsoft.com/cbernier/2017/05/19/windows-information-protection-explained-windows-10-creators-update/
That’s it, if you’re not utilizing Windows Information Protection today, I highly encourage everyone to look into the benefits of protecting corporate information across personal and corporate owned devices with Intune, including Windows, iOS, and Android.


