UPDATE: as of December 2022, Android Enterprise token lifetimes have increased from 90 days to 65 years, however for shorter lifetimes where autorenewal may be required, the content within this article remains relevant.
This month’s post is a continuation of automation with Intune data using Power Automate and Graph. When managing Android devices utilizing Device Owner enrollment (i.e. Android Enterprise) there are options for enrollment, NFC, QR Code, and Zero Touch. Each enrollment option requires an enrollment token as well and those are displayed in the Microsoft Endpoint Manager (MEM) admin center. With Android Device Owner dedicated (i.e. kiosk) enrollments, MEM Intune provides the option to create enrollment profiles where each has their own enrollment token. Organizations may choose to create multiple profiles for various reasons, however enrollment profiles may be utilized to automatically to add devices to Azure AD dynamic groups. This makes management of devices and targeting policy/apps seamless.
One point of feedback I’ve received is about the token lifetime of 90 days for Device Owner dedicated enrollment profiles. When an enrollment token expires no new devices may be enrolled until the token lifetime is extended (existing enrolled devices are not impacted). Token extensions may be completed in the MEM admin center or through PowerShell. However, why not automate the process? This is exactly what I do in this month’s post.
Let’s get started
Requirements
- Microsoft Endpoint Manager Intune
- Microsoft Power Automate (aka Microsoft Flow)
- Azure Active Directory
Description of the process
The process of renewing token when they near their expiration is as follows:
- Introduce a recurrence trigger where the Flow processes every day.
- Set a timeframe to look for when tokens are about to expire.
- Make a graph call through HTTP.
- Parse the JSON that comes from the output of the Graph call.
- Look for any tokens that expire within 10 days.
- If successful, extend the token for another 90 days.
- Make another Graph call and parse JSON to get the tokens that were extended.
- Send a notification of which tokens were extended to Teams.
Here is the entire Flow we’ll walk through:

Power Automate
Log into Power Automate, i.e. flow.microsoft.com and create a new Flow.
Scheduled run
Insert a Recurrence trigger and modify to run every day at a specific time.
Add to time
We need to set a timeframe for when the token is set to expire. I chose 10 days, and later on we’ll use this value to look and see if tokens are set to expire within 10 days.

Register an app with Azure AD
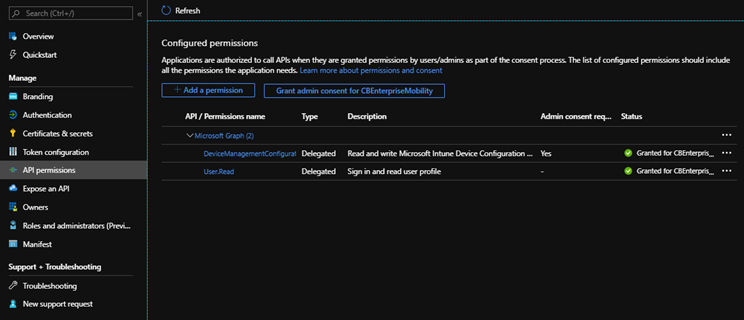
To make Graph calls we need to register an app in Azure AD and grant it the following delegated permissions: DeviceManagementConfiguration.ReadWrite.All
We can pull all the information to build the query from: https://docs.microsoft.com/en-us/graph/api/intune-androidforwork-androiddeviceownerenrollmentprofile-createtoken?view=graph-rest-beta
POST https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles/{androidDeviceOwnerEnrollmentProfileId}/createToken
Content-type: application/json
Content-length: 35
{
“tokenValidityInSeconds”: 7776000
}
This API is under /beta and may change, please make note of this. Note if the graph endpoint above isn’t working, utilize the following for GET: https://graph.microsoft.com/beta/deviceManagement/androidForWorkEnrollmentProfiles
Add a Redirect URI, I pull this from the connector I created in a previous post:

Create a client secret to utilize in authentication:

Grant proper API permissions:
Use Graph to query for all Android enrollment tokens
Add an HTTP action and configure as shown in the image below. This is a GET method.
Refer to the Azure AD app registration completed in the previous step to fill in Client ID and Secret.

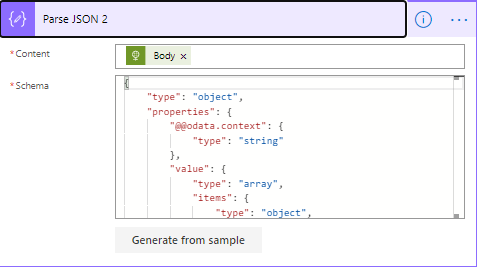
Add a Parse JSON action so we can utilize the values that come back in the GET method.
Choose the “Body” of the HTML action and for the Schema, make a Graph call using Graph Explorer by doing the following:
- Sign into Graph Explorer and GET https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles/
-
Choose one profile and append the query above with the ID
- Copy the JSON output and in the Parse JSON action, select “Generate from sample” and past in the JSON and select DONE.
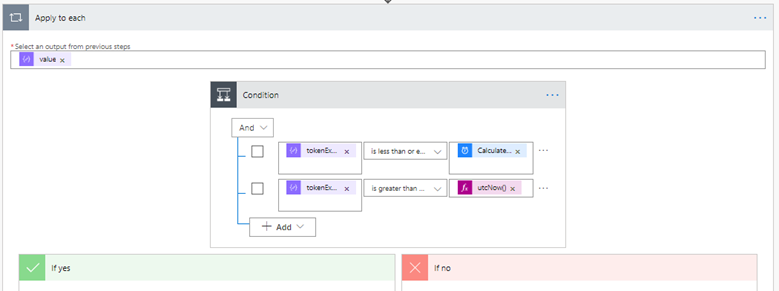
Add a Condition action (this will turn into a Apply to each automatically)
In the first field add tokenExpirationDateTime (this will trigger the Apply to each action) > is less than or equal to > in the second field add “Add to time” output from the action created in the beginning of this post:
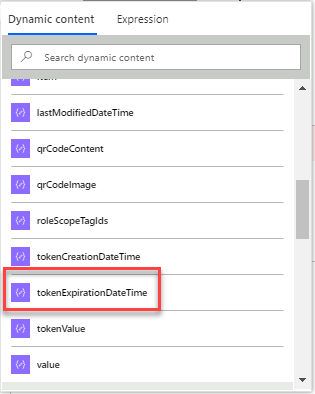
Add an “And” in the condition and in the first field add tokenExpirationDateTime > is greater than or equal to > and in the second field choose utcNow() from Expression.
What the condition is doing is checking to see if the date of the token expiration falls within 10 days, if not do nothing, if yes, we extend the token with actions under “If yes” which I cover next.
Extending the Android enrollment token
The first step if the condition is true is to update the tokens that expire within 10 days. Do this by adding an HTTP action and configuring as shown in the image below:

Next we want to validate the tokens that were extended by calling Graph. We do this by adding two actions, an HTTP action and a Parse JSON action.
The HTTP action is identical to the one we created earlier, however append it by adding the ID of the token from the dynamic content list. Use the same process for Parse JSON as we did in the previous step as well. This step will only pull the tokens that were extended.

Lastly, I’d like to know when enrollment tokens were extended so I send messages to Teams.
The reason why we query for the tokens that were extended in the step above is because we need to utilize that output to populate the Teams messages.

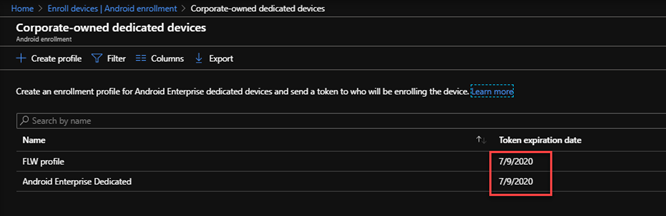
I have a couple tokens I set to expire in 5 days (in fact you can set any expiration date within 90 days directly from the MEM admin center if needed. It’s good for testing as well.):

I ran the Flow and here are the results posted to Teams, however you can send to email, SMS, SharePoint, etc. if you prefer, just look for the diffrent templates in Power Automate:

And in the Intune console:
One last item
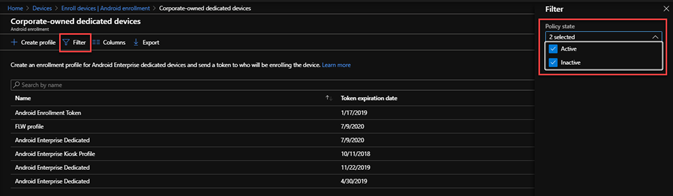
If you’d rather view and extend Tokens by hand in the UI, you can do so by selecting Filter then Inactive which shows all expired and active tokens.
Note: if you’re printing the QR code or sending it via email, using the token with Knox Mobile Enrollment (KME), Android Enterprise Zero Touch, or are using the enrollment token anywhere else, all locations will need to be updated with the new token code after the extension. This is behavior of the Android Enterprise API.
That’s it, utilizing Power Automate and Microsoft Graph we have automated extending Android enrollment token expiration dates and posted the results to Teams.

Thank you for sharing it! But one question, does the qr code creates a new one or just keeps the original?
LikeLike
Keeps the original token.
LikeLike
It doesn’t keep the original token based on our testing.
LikeLike
Correct, this is by design. However, if you’re scanning QR from the portal you’ll be ok. Also this method retains the token profile so if you’re utilizing Azure AD dyanmic groups orgs will want to maintain the token profile name.
LikeLike
Please elaborate on the statement ‘if you’re scanning QR from the portal you’ll be ok’.
We have older devices that do not support QR codes and require input of the 20+/- character token code.
How does the token code expire and not the QR code? Are you saying that the QR code references the profile and not the token code?
I want to avoid having to re-issue a new token code / QR code every 90 days to multiple locations across North America.
LikeLike
You’ll need to renew the token every 90 days regardless of method utilized to renew it.
LikeLike
Great article, I love automation 🙂 Unfortunately or luckily, the enrollment tokens are now valid up to 65 years.
LikeLike
I know, it’s exciting! I’m one of the people behind the change working on all our customer’s behalf 🙂
LikeLike